CCTV News: On January 17, the National Internet Emergency Center CNCERT released a report, announcing the details of the US's cyber attack on an advanced materials design institute in my country. Previously, an announcement was issued on December 18, 2024 that two cyber attacks on large technology companies in the United States were discovered and dealt with.
1. Cyber attack process
(I) Using vulnerabilities to attack intrude
On August 19, 2024, the attacker used the unit's electronic file system injection vulnerability to intrude the system and stole the system administrator account/password information. On August 21, 2024, the attacker used the stolen administrator account/password to log in to the management background of the attacked system.
(II) The software upgrade management server was implanted in the backdoor and Trojan program
At 12:00 on August 21, 2024, the attacker deployed the backdoor program and a customized Trojan program to receive stolen data in the electronic file system. To evade detection, these malicious programs exist only in memory and are not stored on the hard disk. The Trojan program is used to receive sensitive files stolen from the personal computer of the involved unit, with the access path of /xxx/xxxx?flag=syn_user_policy. The backdoor program is used to aggregate the stolen sensitive files and transfer them to the overseas country. The access path is /xxx/xxxStats.
(III) A large-scale personal host computer was implanted with Trojans
On November 6, 2024, November 8, 2024 and November 16, 2024, the attacker used a software upgrade function of the electronic document server to implant the special Trojan program into 276 hosts of the unit. The main function of the Trojan program is to scan sensitive files implanted into the host for stealing. The second is to steal other personal information such as the attacked person's login account secret. Trojan programs can be deleted as soon as possible.
2. Steal a large amount of commercial secret information
(I) Full disk scan of the victim unit host
The attacker used the Chinese IP springboard to log in to the software upgrade management server many times, and used the server to invade the victim unit's intranet host, and repeatedly scan the unit's intranet host hard disk to find potential attack targets and master the work content of the unit.
(II) Purpose clearly targeted theft
From November 6 to November 16, 2024, the attacker used three different springboard IPs to hack the software into the management server and implanted Trojans into the personal host. These Trojans have built-in specific keywords that are highly related to the work content of the victim unit. After searching for files containing specific keywords, the corresponding files will be stolen and transmitted to the overseas country. The keywords used in these three stealing activities are different, showing that the attacker has made careful preparations before each attack and is highly targeted. Three secret thefts stole a total of 4.98GB of important commercial information and intellectual property documents.
3. Characteristics of Attack Behavior
(I) Attack time
Analysis found that the attack time was mainly concentrated between 22:00 Beijing time and 8:00 the next day, compared with 10:00 to 20:00 in the daytime of the United States. The attack time was mainly distributed from Monday to Friday in the United States, and there was no attack on major holidays in the United States.
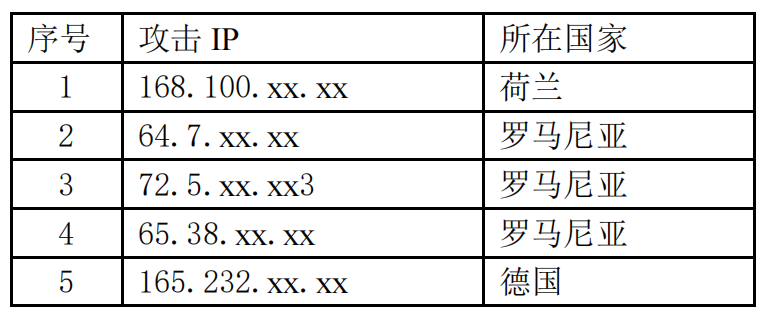
(II) Attack resources
The five springboard IPs used by the attacker are not duplicated at all. They are located in Germany and Romania, reflecting their high anti-traceability awareness and rich reserves of attack resources.
(III) Attack weapons
First, it is good at using open source or general tools to disguise and avoid traceability. The backdoor program found in the server of the unit involved this time is an open source general backdoor tool. In order to avoid being traced, attackers use open source or general-purpose attack tools in large quantities.
Secondly, important backdoors and Trojan programs are only run in memory and are not stored in hard disk, which greatly increases the difficulty of my analysis and discovery of their attack behavior.
(IV) Attack method
After the attacker attacked the unit's electronic file system server, he tampered with the system's client distribution program, and delivered Trojan programs to 276 personal hosts through the software client upgrade function, quickly and accurately attacked important users, and carried out information collection and stealing. The above attack methods fully demonstrate the powerful attack ability of the attack organization.
IV. Some springboard IP list