CCTV News: On January 17, the National Internet Emergency Center CNCERT released a report, announcing the details of the US's cyber attack on a large high-tech enterprise in my country's smart energy and digital information. Previously, an announcement was issued on December 18, 2024 that two cyber attacks on large technology companies in the United States were discovered and dealt with.
1. Cyber attack process
(I) Use mail server vulnerabilities to intrude
The company's mail server uses Microsoft Exchange mail system. The attacker used two Microsoft Exchange vulnerabilities to attack, first using a certain user forged vulnerability to attack a specific account, and then using a certain deserialization vulnerability to attack again to achieve the goal of executing arbitrary code.
(II) Implanting highly concealed memory Trojans on the mail server
To avoid being discovered, the attacker implanted two attack weapons in the mail server, which only runs in memory and is not stored on the hard disk. It uses virtualization technology, and the access paths of the virtual are /owa/auth/xxx/xx.aspx and /owa/auth/xxx/yy.aspx. The main functions of attack weapons include sensitive information theft, command execution, and intranet penetration. The intranet penetration program evades security software detection through obfuscation and forwards attacker traffic to other target devices, achieving the purpose of attacking other intranet devices.
(III) Exploiting more than 30 important devices in the intranet
The attackers used the mail server as a springboard and used intranet scanning and penetration to establish a hidden encrypted transmission tunnel in the intranet, log in and control the company's more than 30 important devices through SSH, SMB and other methods and steal data. Including personal computers, servers and network equipment; the controlled servers include mail servers, office system servers, code management servers, test servers, development management servers and file management servers. In order to achieve persistent control, the attacker implanted an attacking and stealing weapon that can establish a websocket+SSH tunnel in the relevant servers and network administrator computers, realizing hidden forwarding and data theft of attacker instructions. To avoid being discovered, the attack espionage program disguised as WeChat related program WeChatxxxxxxxx.exe. The attacker also implanted two modular malicious programs using PIPE pipelines to communicate between processes in the victim server, realizing the construction of the communication pipeline.
2. Steal a large amount of trade secret information
(I) Steal a large amount of sensitive email data
The attacker used the email server administrator account to perform email export operations. The target of the stealing secrets was mainly the company's senior management and important department personnel. When the attacker executes the export command, the time interval for exporting the emails is set. Some accounts have all emails exported, and many accounts have their emails exported according to the specified time interval to reduce the amount of espionage data and reduce the risk of being discovered.
(II) Stealing core network equipment account and configuration information
The attacker attacked the computers of three network administrators of the company and frequently stole the company's core network equipment account and configuration information. For example, on May 2, 2023, the attacker used the proxy server (95.179.XX.XX) located in Germany as a springboard, and then used the email server as a springboard to attack the company's network administrator computer, and stole sensitive files such as "network core device configuration table", "core network device configuration backup and inspection", "network topology", "computer room switch (core + aggregation)", "operator IP address statistics", "requests for purchasing Internet control gateways".
(III) Stealing project management files
The attacker frequently steals the company's related development project data by attacking the company's code servers, development servers, etc. For example, on July 26, 2023, the attacker used the proxy server (65.21.XX.XX) located in Finland as a springboard. After attacking the company's mail server, he used it as a springboard to frequently access the backdoor attack weapons implanted in the company's code server, stealing up to 1.03GB of data. To avoid being discovered, the backdoor program disguises itself as the file "tip4XXXXXXXX.php" in the open source project "Zen Tao".
(IV) Clear attack traces and conduct anti-evidence analysis
To avoid being discovered, after each attack by an attacker, the attacker will clear the attack traces in the computer log and delete the temporary packaged files generated during the attack stealing process. The attacker will also view the system audit log, historical command records, SSH-related configurations, etc., in an attempt to analyze the evidence collection of the machine and combat network security detection.
3. Characteristics of Attack Behavior
(I) Attack time
Analysis found that the attack activity was mainly concentrated between 22:00 Beijing time and 8:00 the next day, compared with 10:00 to 20:00 in the daytime of the United States. The attack time was mainly distributed from Monday to Friday in the United States, and there was no attack on major holidays in the United States.
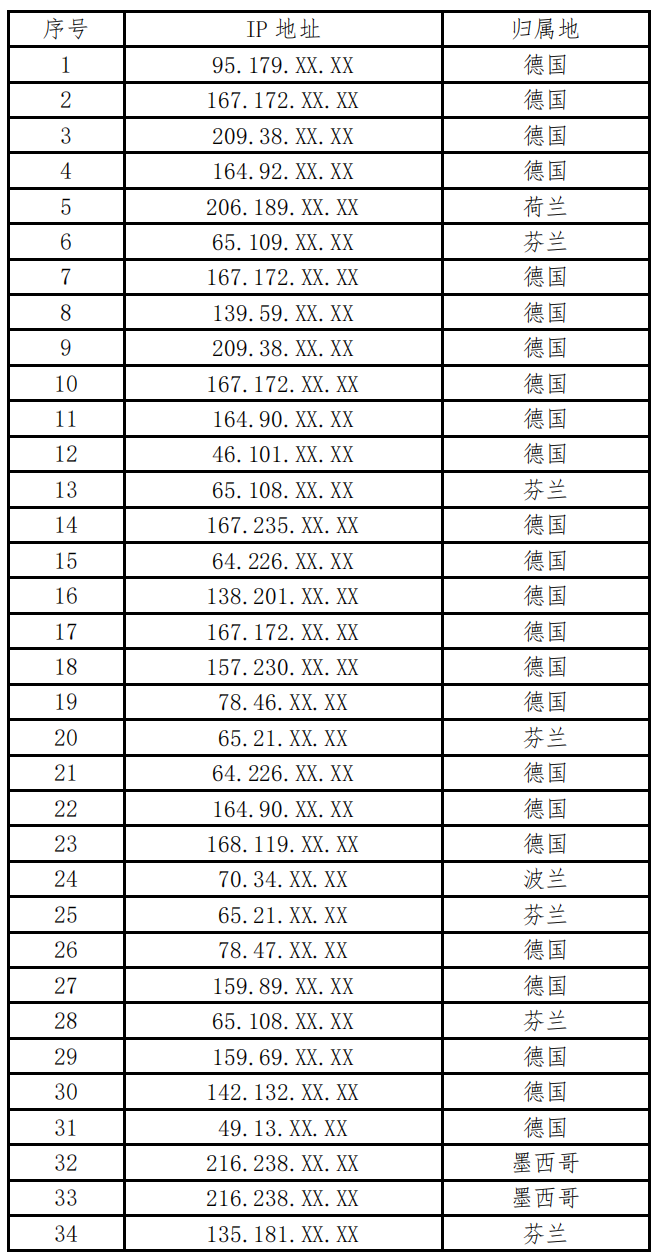
(II) Attack resources
From May 2023 to October 2023, the attacker launched more than 30 cyber attacks. The overseas springboard IPs used by the attacker are basically not repeated, reflecting its high anti-traceability awareness and rich reserves of attack resources.
(III) Attack Weapons
The two modular malicious programs for PIPE pipeline process communication implanted by the attacker are located under "c:\\windows\\system32\\". They use the .net framework. The compilation time is erased, with a size of tens of KB, mainly TLS encryption. The main functions of attack weapons implanted in the mail server's memory include sensitive information theft, command execution, and intranet penetration. The attack and stealing weapon implanted in related servers and network administrator computers can use the https protocol to establish a websocket+SSH tunnel and will return to a domain name controlled by the attacker.
IV. Some springboard IP list